- +61 7 3374 2877
- Email Us
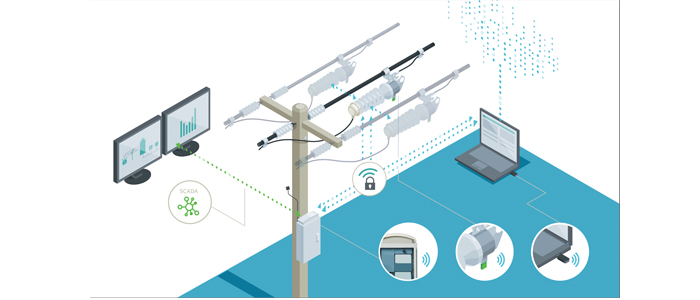
In our hyperconnected world, protecting energy networks against cyber threats is mission critical. Cybersecurity discussions often delve into complicated and confusing technicalities. However, the practice of safeguarding digital systems and information from unauthorised access, attacks, and data breaches is imperative for those responsible for managing the complex digital infrastructure.
Imagine the utility system as a highly fortified stronghold and its personnel as digital gatekeepers. Their primary duty is to ensure that only individuals with the appropriate authorisation can access specific areas within this digital fortress. This is precisely where the concept of Role-Based Access Control (RBAC) comes into play and warrants a more profound examination.
RBAC can be thought of as a sophisticated key-management system, where each individual is issued a unique key that can unlock only the doors assigned to their roles. Let’s dissect this in a more technically inclined manner:
Authorisation Mechanism Based on Responsibilities and Least Privilege
RBAC’s core principle revolves around granting access privileges to authenticated users based on their assigned roles and the principle of least privilege. This approach ensures that users are only given the minimum access required to perform their specific tasks, mitigating the risk of unauthorised access and security breaches.
Trust in Data Integrity
In the digital realm, RBAC functions analogously to a key ring with many different keys for different doors. It enables data recipients to verify the authenticity and integrity of incoming data by scrutinising digital signatures or checksums. This ensures that data from trusted sources is reliably authenticated and tamper-proof.
Role Definition and Customisation
RBAC allows for the precise definition of user roles, making it possible to categorise individuals into distinct functional categories, each with a unique set of permissions and responsibilities. This customisation facilitates granular access control.
Fine-Grained Access Control
With RBAC, administrators can meticulously tailor permissions for each role, specifying the precise functions and resources accessible to users within their roles. This granularity ensures that access is aligned with operational requirements.
Efficient User Management
RBAC streamlines user provisioning and de-provisioning. When a new user joins, administrators simply assign them a predefined role, automating the provisioning of permissions and access rights.
Now, let’s delve into how RBAC benefits energy network operators: